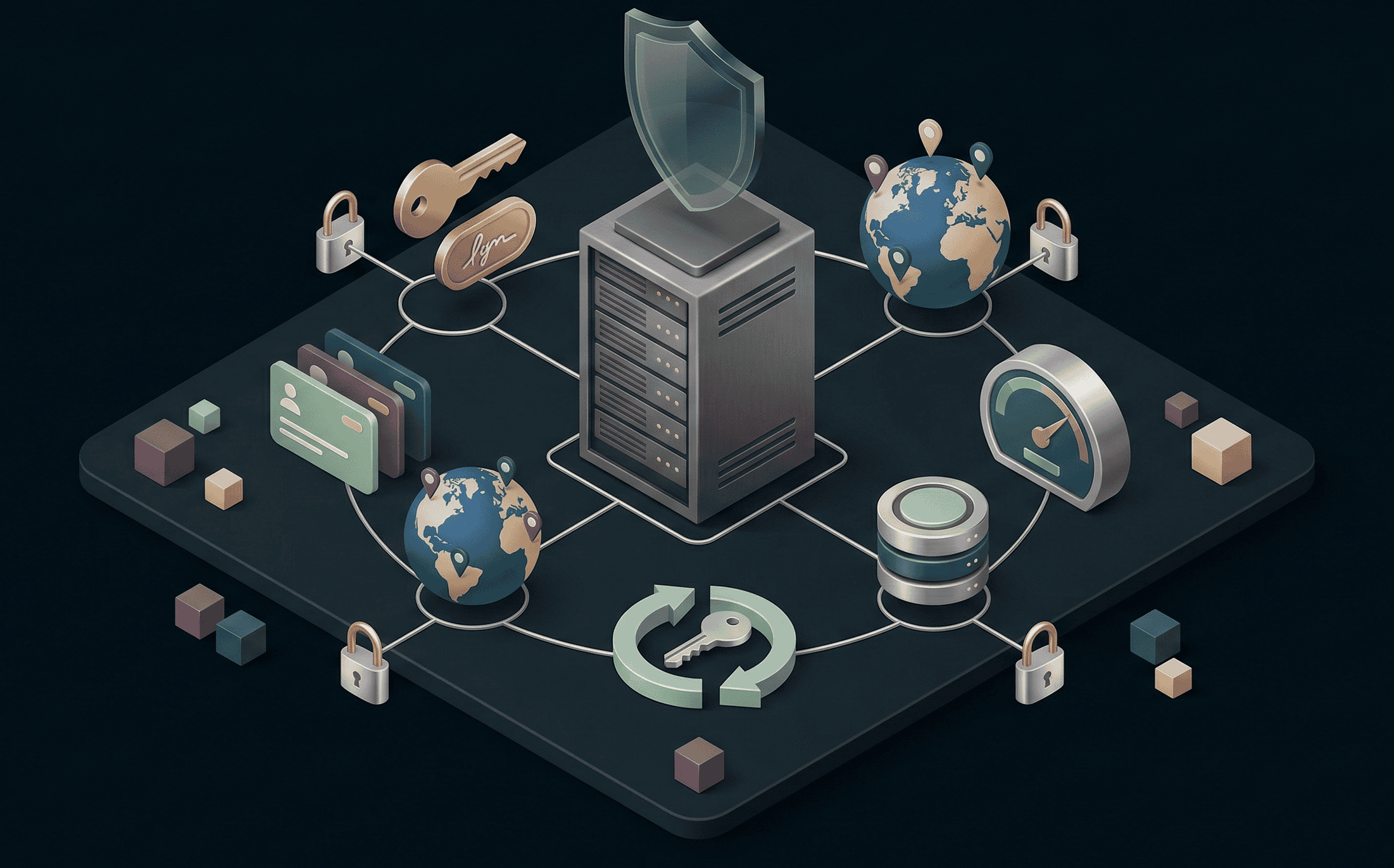
Comprehensive User Authentication
2FA (TOTP, SMS, email), biometric login (Face ID, Touch ID), FIDO2 hardware key support (YubiKey, Titan), and anti-phishing protections. Login monitoring, IP whitelisting, and device management built into the user security dashboard.