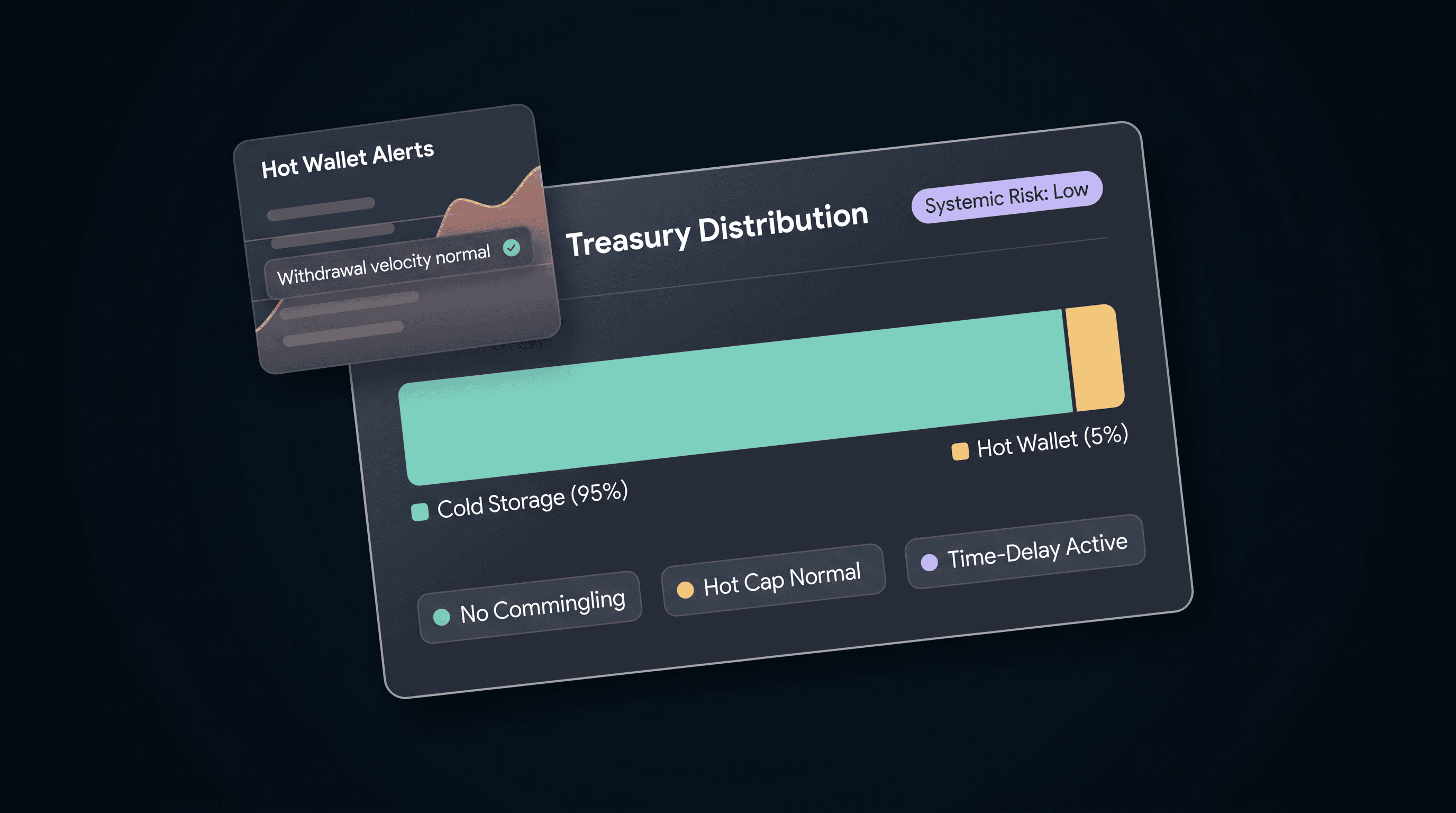
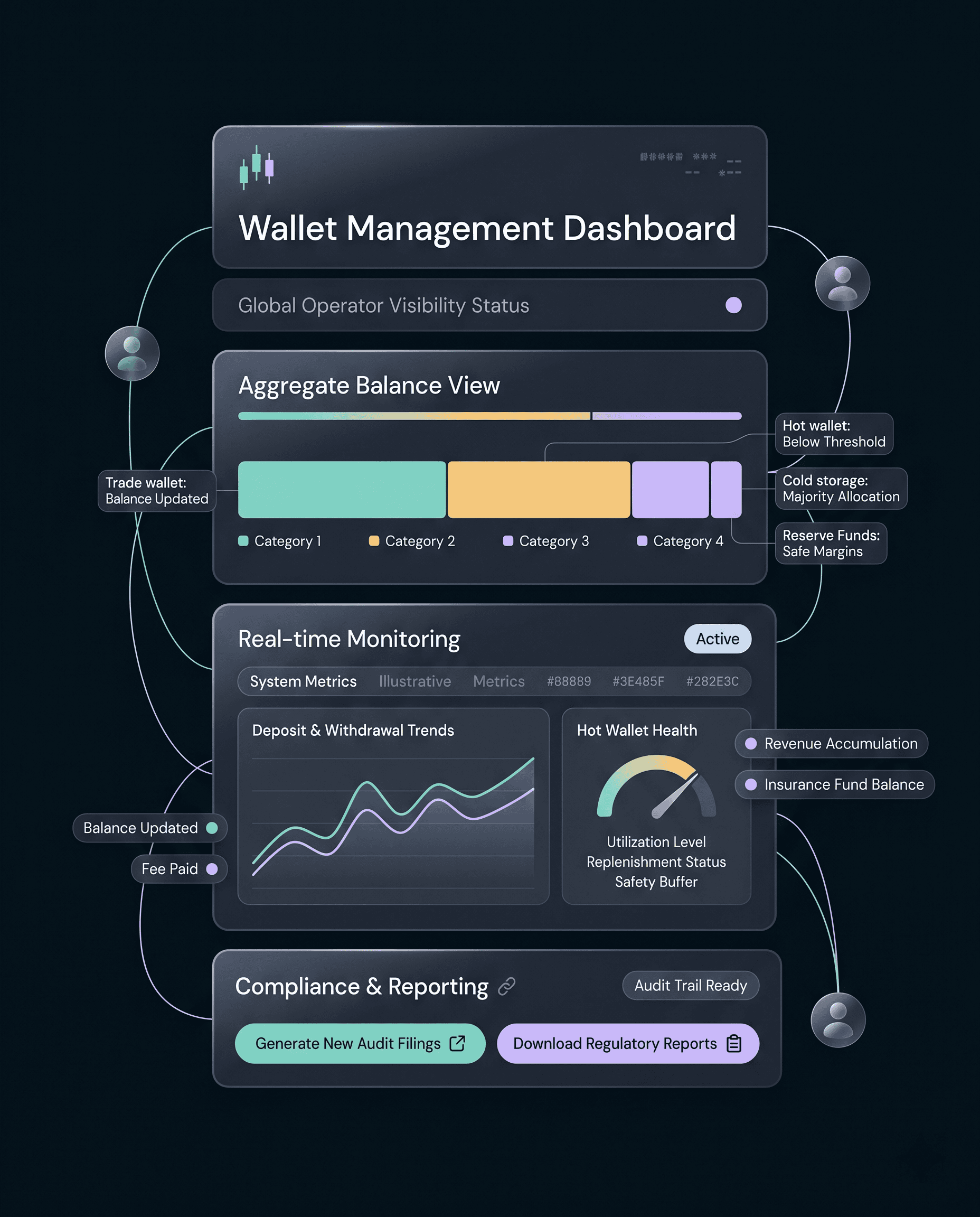
Identification of Systemic Risk
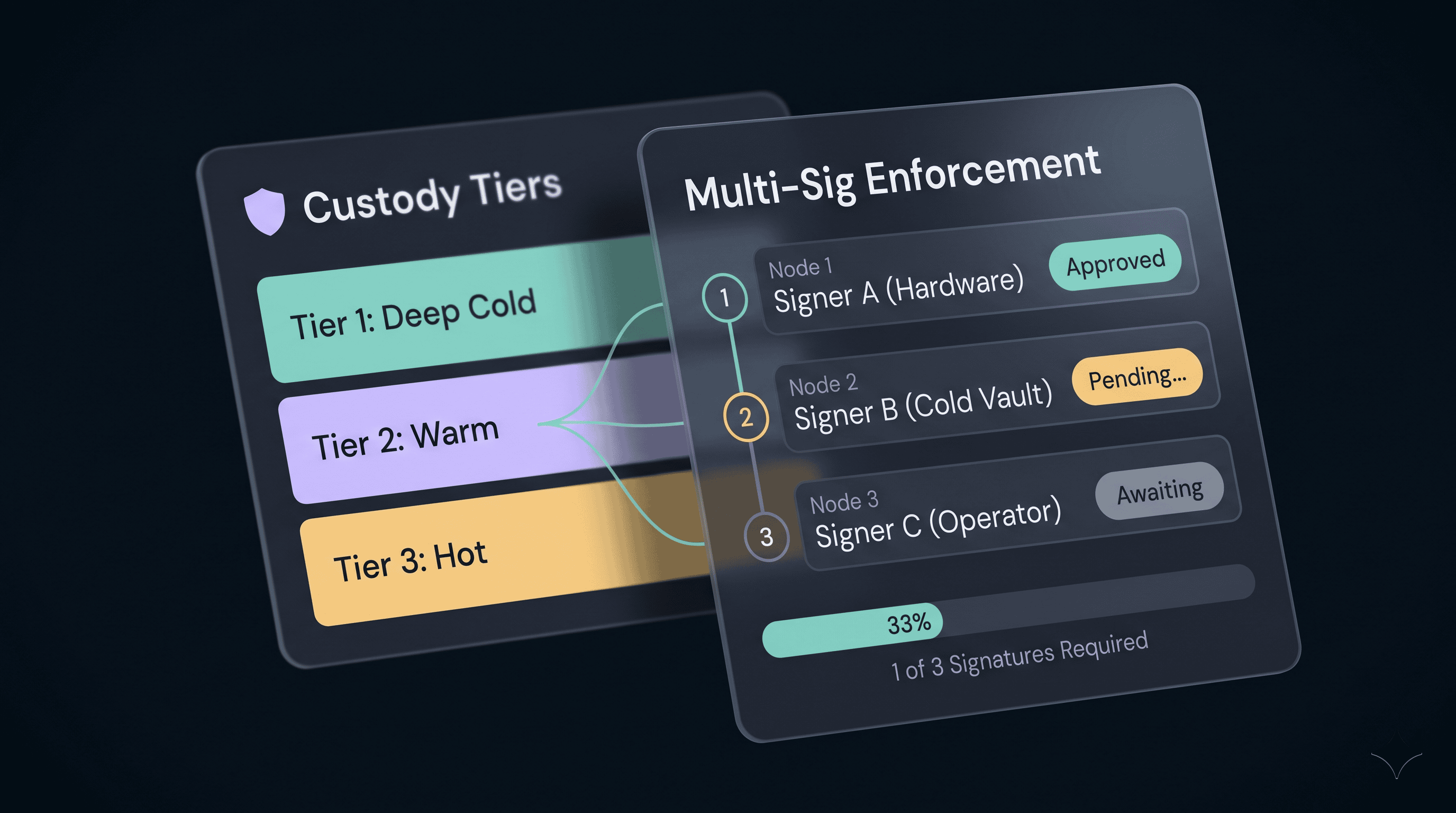
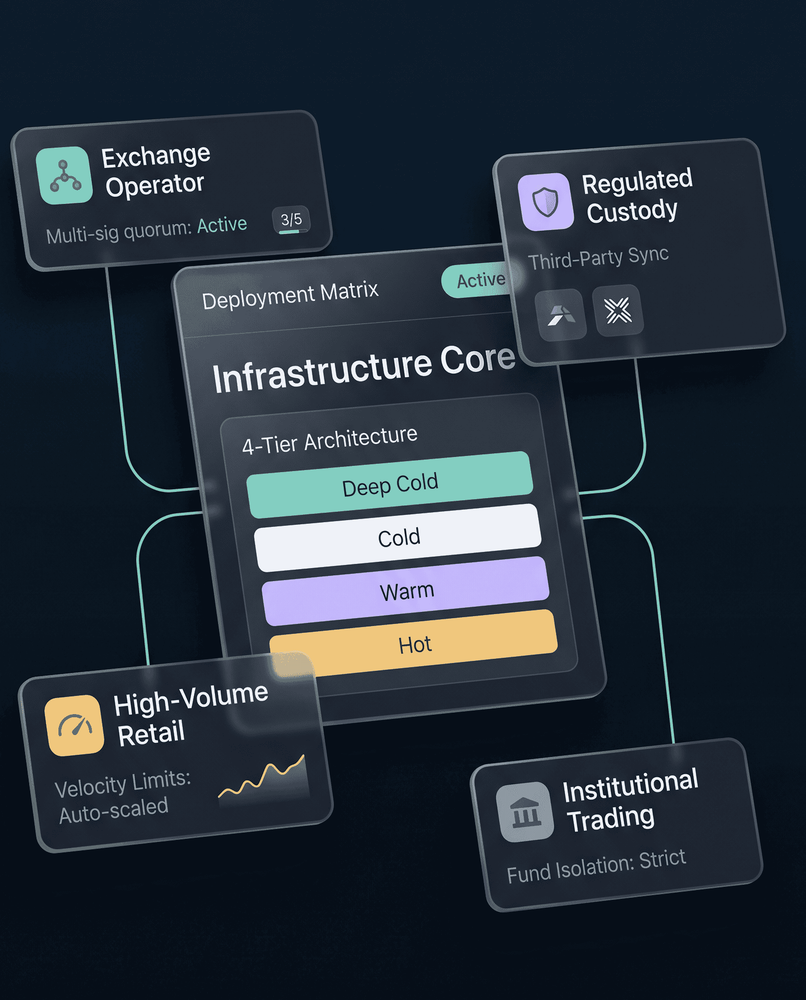
Most exchange security incidents trace back to the same root causes: hot wallets holding too much capital, no time-delay controls on warm-to-hot transfers, cold storage without quorum authorization, and user funds commingled with operator treasury.